Why KYB is no longer enough to stop B2B fraud
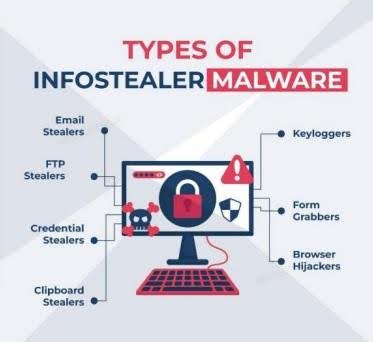
The new face of B2B fraudFraud is a constant game of cat and mouse between security teams and criminal networks. Nefarious new tactics emerge, businesses respond, and the cycle repeats. So, unsurprisingly, fraud in digital ecosystems has evolved to overcome existing checks and safeguards. Instead of breaking systems, criminals now move through them – using…